Businesses must take proactive measures to safeguard the sensitive data they hold and ensure the resilience of their information security infrastructure, especially to known active exploits of vulnerabilities. Two common approaches to test the security of systems are penetration testing and vulnerability scanning. We previously covered some tips and tricks for scoping penetration testing: 8 Questions Directors Should Ask About Penetration Tests. Now there is a greater problem facing organisations when trying to decide on the right product or vendor.
The problem?
Vulnerability scanning is being sold or coined as “penetration testing” when in reality, it only provides a quick, external view of security. In actuality, there may be far greater issues and vulnerabilities that an external scan would not be able to detect.
Why is it being sold under the wrong label?
Profits! Vulnerability scanning is much easier to do and can even be automated. Organisations have latched on to the term “penetration testing” and so blurring the line between the two types of testing, and some cheeky sales tactics, means vendors can undercut true penetration testing providers with supposed “better value”.
Why is “penetration testing” the hot term?
Penetration testing of applications and systems is a necessity for many regulatory bodies and international standards. Well known information security standards ISO 27001, CPS 234 and NIST SP 800-53 all require the appropriate testing of systems. Utilising vulnerability scanning, penetration testing or both may satisfy the requirements for a regulated organisation and will provide greater insight into key security risks at the very least.
While both types of testing are crucial components of a robust cyber security strategy, they serve distinct purposes and have their own sets of advantages and limitations. This article aims to shed light on the differences between these two methodologies, what you are actually getting with each, their respective benefits and drawbacks, and key terms to look out for to know if you are being sold the right product.
Vulnerability Scanning
Vulnerability scanning is typically an automated process that utilises specialised software to identify known security vulnerabilities within systems, networks, or applications. It typically scans the target environment from an external/public perspective, compares the results against an extensive database of registered vulnerabilities such as the Common Vulnerabilities and Exposures (CVE) database, and generates a report detailing the identified weaknesses.
Benefits of Vulnerability Scanning:
- Rapid Discovery: Vulnerability scanning is a fast and efficient way to identify known security issues across a wide range of assets in the same manner a threat actor typically would.
- Cost-Effective: Automated vulnerability scanning tools can be more cost-effective compared to penetration testing, especially for continuous monitoring and regular assessments.
- Easy Implementation: Vulnerability scanning tools are user-friendly and can be deployed without extensive technical expertise and are sometimes managed by risk or governance teams as opposed to IT.
Disadvantages of Vulnerability Scanning:
- Limited to Known Vulnerabilities: Vulnerability scanning relies on a database of known vulnerabilities, meaning it may miss new or undiscovered security flaws.
- False Positives and Negatives: Automated scans can generate false positives, incorrectly flagging legitimate applications or systems as vulnerable, or miss certain vulnerabilities due to the external/public assessment method.
- Lack of Context: Vulnerability scanning may not provide insight into the potential impact of identified weaknesses on an organisation’s overall security posture. Vulnerability testing also lacks critical information into how a vulnerability can be realistically exploited, requiring further investigation.
- False Advertising: In recent years, vulnerability scanning has been advertised by some as a type of penetration testing at a much lower cost. This type of advertising technique is used to gain competitive advantage while offering an automated and low-cost product with false promises.
Penetration Testing
Penetration testing, often referred to as ethical hacking, is a methodical and controlled approach to assessing the security posture of a system, network, or application. It involves simulating real-world cyber attacks to identify exploitable weaknesses and potential entry points for malicious actors.
How does it work?
Skilled cyber security professionals, known as penetration testers or ethical hackers, conduct both external and internal tests to emulate the tactics, techniques, and procedures (TTPs) of actual attackers. Penetration testers utilise databases such as OWASP and CVE alongside other databases such as the Known Exploited Vulnerabilities (KEV) Catalogue to provide context on vulnerabilities and whether the system can be practically compromised.
Benefits of Penetration Testing:
- Realistic Assessment: Penetration testers are not robots. Penetration testing offers a hands-on evaluation of security measures, mimicking the tactics used by malicious actors. This leads to a more accurate depiction of an organisation’s security posture and gives keen insights into how a hacker may leverage certain vulnerabilities and escalate privileges in the context of your specific systems and configuration.
- Comprehensive Analysis: The process helps identify not only individual vulnerabilities but also potential chain reactions that may arise when multiple weaknesses are combined.
- Risk Prioritisation: Penetration testing provides insights into the criticality of identified vulnerabilities, enabling organisations to prioritise remediation efforts based on their potential impact to their internal data and systems.
- Compliance Requirements: Many regulatory frameworks and industry standards mandate regular penetration testing as part of a comprehensive security program.
- Provides Context: Penetration testing allows for the ethical hacker to thoroughly analyse how vulnerabilities in your systems may be exploited to attack your organisation. This greatly eliminates the concerns for any false positives or false negatives and also provides context by showing what data the attacker could gain from utilising their exploits and how you can go about remediating those issues.
Disadvantages of Penetration Testing:
- Cost and Time-Intensive: Penetration testing can be resource-intensive, requiring skilled personnel, specialised tools, and significant time investments if the scope of the test is not carefully planned.
- Limited Scope: Penetration tests often focus on specific targets or applications due to the above costs, potentially missing vulnerabilities present in other areas. Organisations should adequately understand their threat landscape and include the right key systems in the scope of penetration testing, cycling the targets over a multi-year program.
- Results can vary: Depending on experience, limit of scope and how thorough the penetration tester is, results from a penetration test can vary drastically. It is imperative to appropriately check penetration testers for their experience, knowledge and price point before proceeding and consider variation in the testing provider each year.
Comparison Summary
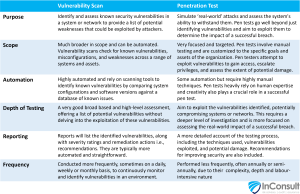
Here’s a breakdown of the key differences between vulnerability scans and penetration tests:
Using Penetration Testing and Vulnerability Scanning in Tandem
The most effective approach to enhance an organisation’s testing capability involves utilising both penetration testing and vulnerability scanning in tandem. This will create an extensive vulnerability management program which will allow your security team to appropriately identify, prioritise, assess, remediate, verify and report any concerning vulnerabilities.
By combining these methodologies, organisations can leverage their respective strengths while compensating for their limitations. This will typically begin with conducting a vulnerability scan to rapidly identify and address known security issues across a broad range of assets.
Vulnerability scanning also provides ongoing, low cost vulnerability checking between scheduled penetration tests. This helps eliminate low-hanging fruit and reduces the overall attack surface. This can then be followed up with penetration testing to gain deeper insight into the organisation’s security posture. Penetration tests can uncover more sophisticated vulnerabilities and potential chain reactions, providing a realistic assessment of the organisation’s defences. It is imperative to implement regular monitoring, vulnerability scans and periodic penetration testing to ensure ongoing security hygiene and to identify any emerging threats.
The Human Factor
It is important to recognise that penetration testing and vulnerability scanning are effective ways to improve the security of your systems, but they do not account for all cyber security incidents. The NDB report of July-December 2022 shows how the majority of incidents are a result of human error. This is not accounted for in a vulnerability scan and may be be out of scope in a penetration test. Incorporating proper governance, risk management, phishing campaigns, vulnerability scanning and appropriate training of staff are all important to building a strong information security framework.
Conclusion
Both penetration testing and vulnerability scanning play critical roles in assessing your organisation’s information security infrastructure but they are not the same. While penetration testing offers a realistic evaluation of security measures and identifies intricate weaknesses, vulnerability scanning provides rapid identification of known vulnerabilities across a broad range of assets. By using these methodologies in tandem, organisations can enhance their ability to identify and address potential weaknesses, strengthen their overall cyber security defences, ensure compliance with regulation and safeguard their valuable assets against ever-evolving cyber threats.
How can we help?
We are here to help strengthen cyber resilience. We can provide clear insights into what your organisation needs, whether that be vulnerability scanning, penetration testing or risk management as a whole. Our cyber risk management capabilities include designing and developing a cyber risk management framework and a wide range of response plans to enhance your cyber resilience capabilities. Our cyber risk management services include:
- Vulnerability scanning
- Cyber Security Gap Analysis
- Regulation compliance advice
- Cyber Risk Governance Framework Reviews
- Cyber Risk Governance Framework Development
- Third-Party Vendor Review and Cyber Risk Analysis
- Cyber Risk Awareness Training and Internal Campaigns
- Post-Cyber Incident Review
- Email Phishing Campaigns
- Cyber Incident Response
- Crisis Team Familiarisation Training
Be more resilient to a wide range of cyber risks and get relevant insight into how to protect your systems by contacting us to discuss how we can help strengthen your cyber resilience framework.